Linux depends upon administrative user permission. Without the elevated permission of root, many commands could not be run. For distributions, such as Red Hat, gaining root permissions means changing to the root user with the command su. Other distributions, such as Ubuntu Linux, opt for a different route. That route is sudo. By taking advantage of the sudo system, an administrator gains far more control over who can do what on a system. An added benefit of using the sudo command is that all sudo incidents are logged (Red Hat-based systems log to /var/log/secure whereas Debian-based systems log to /var/log/auth.log).
Say, for example, you want to give certain users permission to use a certain command, without having to enter their sudo password. With sudo you can do that. You can also join users into groups, to make controlling who can do what much easier.
Now that I have your interest piqued, how do you manage/configure sudo on your Linux machine? The answer is simple…sudoers. In the file /etc/sudoers, you’ll find everything you need to wrestle control over sudo.
A word of caution
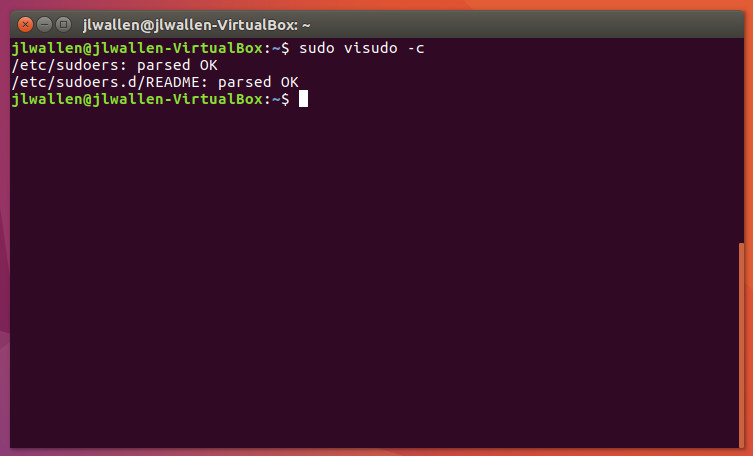
Taking on the /etc/sudoers file must be done with care. You should never open that file with a standard text editor (such as nano or vi). Instead, use the built-in visudo tool. This tool will parse the file to see if there are any problems. Once you’ve made changes to the file, you can even run the command sudo visudo -c to run a second automatic parse of the file. Should visudo find issues, fix them immediately before closing your terminal (otherwise, you can wind up locked out of all command that require sudo (trust me, I did this once…it’s no fun)
It is also important to understand:
-
The sudo binary is setuid root, which means that when any user runs a command through sudo, they are instantly granted root permissions. Because of this, you must take extra precaution when working with the /etc/sudoers file; otherwise, you could find your system at serious risk.
-
The sudo command reads the sudoers file in top-to-bottom order. In other words, the last line in /etc/sudoers will overwrite previous conflicts with the setup. Because of this, you should always enter your new lines at the bottom of each /etc/sudoers section.
-
The sudo command includes a number of defaults that can be set within /etc/sudoers. To find a listing of these defaults, issue the command sudo -L.
Now that you clearly understand the importance of editing /etc/sudoers with visudo, let’s take a look and see what you can do.
The file
There are a few sections of the sudoers file you need to know about:
-
Defaults: These are the default variables for sudo (remember, sudo -L is your friend)
-
Alias: You can create aliases for host, user, and commands
-
User privilege: This is where you specify user privilege
-
Groups: This is where you define groups
You may be surprised to find out the default sudoers file is only 31 lines long (at least in Ubuntu 16.10). It’s not overly complicated, nor is it much of a challenge to understand. However, understanding the breakdown of user privilege lines is very important. The structure of these lines is:
user host=(accounts) commands
The breakdown of this line is:
-
user: The account for which the privilege will be associated
-
host: The system from which the account is able to run these sudo commands (sudoers can be shared across systems)
-
accounts: The other accounts on the machine for which the user running sudo can act
-
commands: The commands the user can run as sudo
If you issue the command sudo visudo, the default /etc/sudoers file will open. In that file, there will only be one line under user privilege. That line is:
root ALL=(ALL:ALL) ALL
According to our breakdown, that command means the root user from all hosts from any account can run all commands.
Aliases
Before we get into adding user permission entries to sudoers, it is important to understand how aliases work. Sudoers aliases come in the form of:
-
User_Alias — specifies a group of users by username
-
Runas_Alias — specifies a group of users by UID
-
Host_Alias — specifies a list of hostnames
-
Cmnd_Alias — specifies a list of commands and directories
A typical alias looks like:
User_Alias USERS = bethany, jamal, morgan, josh
The above alias would include bethany, jamal, morgan, and josh with the alias named USERS. You can also include groups with aliases, such as:
User_Alias ADMINS = %admin
The percent sign indicates to sudo that admin is a system group. To include netgroups, you would prefix the group name with the + symbol. You can also exclude users from an alias by prefixing their name with the ! symbol. Say, for instance, you want to create an alias for restricted users, based on previous aliases. Say users bethany, jamal, morgan, josh, and jonathan are all members of the ADMINS alias, and you want to create an alias for WEBMASTER that does not include the user jonathan. Instead of entering every user, to be included, you could add the admin group and then exclude jonathan like so:
User_Alias WEBMASTER = ADMINS, !johnathan
That’s how aliases work.
Adding entries
Remember, to edit the /etc/sudoers file, we do so with the command sudo visudo.
Our example will be to enable certain users to shutdown the system without having to enter a password. To do this, we will first create a User_Alias for ADMINS. Under the User alias section, add the line:
User_Alias ADMINS = usernames
Where usernames is the list of names to be included with the alias.
Next we create a Cmnd_Alias for the shutdown commands. Under the Cmnd alias section, enter this line:
Cmnd_Alias SHUTDOWN = /sbin/poweroff, /sbin/halt, /sbin/reboot
Finally, under the User privilege section (below the default entry of ALL=(ALL:ALL) ALL), enter the following:
ADMINS ALL=(ALL) NOPASSWD: SHUTDOWN
Save the file and then (for added assurance that everything is okay), issue the command sudo visudo -c. You should see the same output as shown in Figure 1.
To test the new sudoers entry, you’ll need to logout and log back in. Once you’ve done that, open up a terminal window and issue the command shutdown -h now as one of the users listed in the user alias ADMINS. Your system should shut down without prompting for a password.
An eye on security
Obviously, with regards to security, this isn’t the greatest example. However, it does perfectly illustrate how powerful sudoers can be. You will certainly want to tailor your sudoers file to meet your admin needs on every level. Most likely, you won’t create an entry that would allow just any user to shutdown the system without entering a password. However, with a keen eye toward security, you can make sudoers work well for you.
Advance your career in system administration! Check out the Essentials of System Administration course from The Linux Foundation.





