Since we first wrote about Docker last August, the open source container project has advanced in numerous ways. Not only did the company behind it officially shed its original dotCloud name and put Docker at the forefront of its focus, but it also raised $15 million in funding and announced partnerships with the likes of Rackspace, OpenStack, Red Hat and Fedora.
 More recently, Docker added another two milestones to its list of accomplishments. First, it released version 0.9, which is particularly notable for two major improvements: execution driversand libcontainer. Second, it got a major boost when Red Hat announced the extension of its application certification program to include containerized applications.
More recently, Docker added another two milestones to its list of accomplishments. First, it released version 0.9, which is particularly notable for two major improvements: execution driversand libcontainer. Second, it got a major boost when Red Hat announced the extension of its application certification program to include containerized applications.
‘First-Class Support’
Docker 0.9 includes numerous bug fixes and continues the project’s focus on “quality over features, shrinking and stabilizing the core, and providing first-class support for all major operating systems,” in the team’s own words.
It’s also a major step towards a stable, production-ready 1.0 release, they note. In fact, the next release — version 0.10 — will be considered the first release candidate for 1.0.
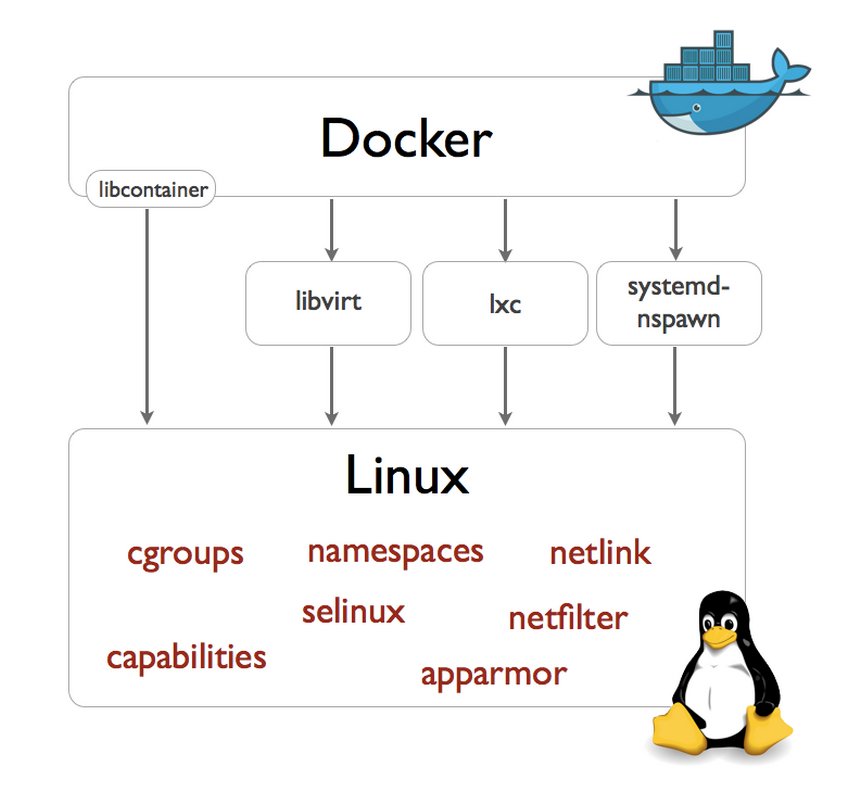
In the meantime, the new version 0.9 introduces an execution driver API that can be used to customize the execution environment surrounding each container, making it possible for Docker to take advantage of isolation tools including OpenVZ, systemd-nspawn, libvirt-lxc, libvirt-sandbox, qemu/kvm, BSD Jails, Solaris Zones and even “good old chroot,” the project team says.
LXC will continue to be available as a driver in its own right as well.
A New Default
Also new in Docker 0.9 is a built-in execution driver based on libcontainer, a pure Go library developed to access the kernel’s container APIs directly, without any other dependencies.
“Thanks to libcontainer, Docker out of the box can now manipulate namespaces, control groups, capabilities, apparmor profiles, network interfaces and firewalling rules -– all in a consistent and predictable way, and without depending on LXC or any other userland package,” the project team explains. “This drastically reduces the number of moving parts, and insulates Docker from the side-effects introduced across versions and distributions of LXC.”
Libcontainer improves stability so much, in fact, that it’s now the default, while LXC is now optional.
‘A Win/Win for Users’
As for Red Hat’s new certification for containerized applications, the rationale was to ensure that application containers built using Red Hat Enterprise Linux will operate seamlessly across certified container hosts, Red Hat explained.
The upcoming release of RHEL 7 and Red Hat’s OpenShift Platform-as-a-Service (PaaS) offering will both be certified container hosts, with Docker as a primary supported container format.
“This announcement is a win/win for users,” Stephen O’Grady, cofounder and principal analyst at RedMonk, told Linux.com. “For Docker users, officially sanctioned access to Red Hat platforms gives that project the ability to target an enormous number of enterprise Linux users and the potentially lucrative market they represent. And for Red Hat, the certification means that for the dramatically expanding Docker community, RHEL is a first-class citizen.”
Red Hat is now offering early access to its partner program whereby ecosystem partners can participate in early testing, integration and feedback of the tools and resources required for containerization prior to the official launch of the certification and partner program later this year. The Partner Early Access Program will run through late spring.
“As the de facto standard in open source container technology, we are pleased to see Red Hat embracing the container movement as a means of application efficiency and consistency across computing footprints,” said Docker CEO Ben Golub.“By offering a container certification on Red Hat Enterprise Linux and Docker, Red Hat is providing the industry’s only standardized, stable platform for commercial container workloads, providing a safe, reliable way to deliver the enterprise applications of the future.”



