Security expert Bruce Schneier says we’re creating an Internet that senses, thinks, and acts, which is is the classic definition of a robot. “I contend that we’re building a world-sized robot without even realizing it,” he said recently at the Open Source Leadership Summit (OSLS).
In his talk, Schneier explained this idea of a world-sized robot, created out of the Internet, that has no single consciousness, no single goal, and no single creator. You can think of it, he says, as an Internet that affects the world in a direct physical manner. This means Internet security becomes everything security.
And, as the Internet physically affects our world, the threats become greater. “It’s the same computers, it could be the same operating systems, the same apps, the same vulnerability, but there’s a fundamental difference between when your spreadsheet crashes, and you lose your data, and when your car crashes and you lose your life,” Schneier said.
Here, Schneier discusses some of these new threats and how to manage them.
Linux.com: In your talk, you say “the combination of mobile, cloud computing, the Internet of Things, persistent computing, and autonomy are resulting in something different.” What are some of the new threats resulting from this different reality?
Bruce Schneier: The new threats are the same as the old threats, just ratcheted up. Ubiquitous surveillance becomes even more pervasive as more systems can do it. Malicious actions become even more serious when they can be performed autonomously by computer systems.
Our data continues to move even further out of our control, as more processing and storage migrates to the cloud. And our dependence on these systems continues to increase, as we use them for more critical applications and never turn them off. My primary worry, though, is the emergent properties that will arise from these fundamental changes in how we use computers — things we can’t predict or prepare for.
Linux.com: What are some of the new security and privacy risks specifically associated with IoT?
Schneier: The Internet of Things is fundamentally changing how computers get incorporated into our lives. Through the sensors, we’re giving the Internet eyes and ears. Through the actuators, we’re giving the Internet hands and feet. Through the processing — mostly in the cloud — we’re giving the Internet a brain. Together, we’re creating an Internet that senses, thinks, and acts. This is the classic definition of a robot, and I contend that we’re building a world-sized robot without even realizing it.
We have lots of experience with the old security and privacy threats. The new ones revolve around an Internet that can affect the world in a direct physical manner, and can do so autonomously. This is not something we’ve experienced before.
Linux.com: What past lessons are most relevant in managing these new threats?
Schneier: As computers permeate everything, what we know about computer and network security will become relevant to everything. This includes the risks of poorly written software, the inherent dangers that arise from extensible computer systems, the problems of complexity, and the vulnerabilities that arise from interconnections. But most importantly, computer systems fail differently than traditional machines. The auto industry knows all about how traditional cars fail, and has all sorts of metrics to predict rates of failure. Cars with computers can have a completely different failure mode: one where they all work fine, until one day none of them work at all.
Linux.com: What will be most effective in mitigating these threats in the future?
Schneier: There are two parts to any solution: a technical part and a policy part. Many companies are working on technologies to mitigate these threats: secure IoT building blocks, security systems that assume the presence of malicious IoT devices on a network, ways to limit catastrophic effects of vulnerabilities.
I have 20 IoT-security best-practices documents from various organizations. But the primary barriers here are economic; these low-cost devices just don’t have the dedicated security teams and patching/upgrade paths that our phones and computers do. This is why we also need regulation to force IoT companies to take security seriously from the beginning. I know regulation is a dirty word in our industry, but when people start dying, governments will take action. I see it as a choice not between government regulation and no government regulation, but between smart government regulation and stupid government regulation.
Linux.com: What can individuals do to make a difference?
Schneier: At this point, there isn’t much. We can choose to opt out: not buy the Internet-connected thermostat or refrigerator. But this is increasingly hard. Smartphones are essential to being a fully functioning person in the 21st century. New cars come with Internet connections. Everyone is using the cloud. We can try to demand security from the products and services we buy and use, but unless we’re part of a mass movement, we’ll just be ignored. We need to make this a political issue, and demand a policy solution. Without that, corporations will act in their own self-interest to the detriment of us all.
To hear more from Schneier, you can watch the complete keynote below.
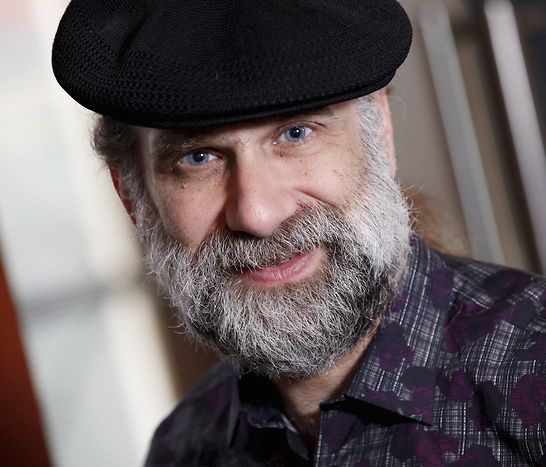
Bruce Schneier is the author of 13 books, as well as the Crypto-Gram newsletter and the Schneier on Security blog. He is also a fellow at the Berkman Klein Center for Internet & Society at Harvard, a Lecturer in Public Policy at the Harvard Kennedy School, a board member of the Electronic Frontier Foundation, an Advisory Board Member of the Electronic Privacy Information Center, and the Chief Technology Officer at IBM Resilient.



