Author: Shashank Sharma
The traditional file permission model, where read, write, and execute permissions are set on each file for the user, group, and others (UGO) has one drawback: It can’t be used to define per-user or per-group permissions. For that, you need to employ access control lists (ACL). Eiciel is a graphical tool that integrates with the Nautilus file manager and allows for easy ACL management.
The UGO model lets you associate only one group with a file. If you try to define read permissions on a file for user Charlie and read and write permissions for user Alexia, and Charlie and Alexia belong to different groups, you’ll see what I mean. With ACLs, you can specify elaborate permissions for multiple users and groups.
Although Eiciel is a GNOME tool, you can run it on KDE as well if you have the necessary GNOME libraries installed. ACL supports is natively available in the 2.6 kernel, and ext2, ext3, XFS, JFS, and ReiserFS filesystems are ACL-capable.
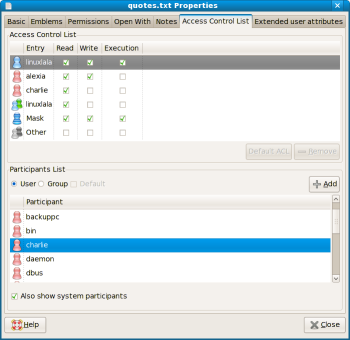
You can install Eiciel from official software repositories of your distribution using apt-get or yum. Once installed, Eiciel is available as a standalone application or as a Nautilus extension, but you’ll have to restart Nautilus before you can take advantage of the extension. After restarting Nautilus with the killall nautilus command, to define ACL entries, right-click on a file and select Properties, then click the Access Control List tab.
ACLs too rely on the traditional read, write, and execute permissions defined for each user and group. To define ACLs for users and groups, add them to the access control list by selecting them from the bottom half of the window and clicking Add. You can then define permissions for each of the users or groups you just added. The user and groups are listed under Entry with three check-boxes corresponding to read, write, and execute. You can thus define any concoction of permissions for the users and groups of your choice.
On Fedora machines, you need to click the Also show system participants check-box to be able to view the various users and groups. This is because Fedora assigns user IDs starting with 500 and not 1000 like other distributions. Ususally, user IDs below 1000 are reserved for system accounts such as root, apache, and ftp.
The User radio button under System Participants is selected by default when you click the Access Control List tab in the Properties window. You can add groups to the ACL by clicking the Group radio button.
The Mask value defines the maximum permissions an ACL entry can have. If you set a permission for a user or group that is not allowed by Mask, Eiciel will put an exclamation mark next to the permission, which means the permission hasn’t been set. So if the mask is set to allow read and write, you can’t define read, write, and execute permissions for any user or group. Eiciel won’t stop you from adding execute permission, but it will use the exclamation mark to show that execute permission has not been set.
Unfortunately, Eiciel doesn’t yet support recursion, so if you have to set ACLs for multiple files or a directory, you’d have to do that individually for each file. The setfacl command, Eiciel’s command-line counterpart, supports recursion, in addition to all the other features offered by Eiciel.
The command setfacl -m u:charlie:rw /home/linuxlala/quotes.txt sets read and write permission for user Charlie. You can also define permissions for more than one user and group at the same time, like so: setfacl -m u:alice:r,u:charlie:rw,g:linuxlala:r /home/linuxlala/quotes.txt. To see if the ACL has been defined properly, use the getfacl command:
getfacl /home/linuxlala/quotes.txt # file: quotes.txt # owner: linuxlala # group: linuxlala user::rwx user:alice:r-- user:charlie:rw- group:r-- group:linuxlala:r-- mask::rwx other::r-x
Despite its ease of use, Eiciel still has a long way to go before it can compete with the setfacl command, while setfacl lacks the charm of Eiciel.
Categories:
- Tools & Utilities
- System Administration
- Security