It was on this day in 1993 that Patrick Volkerding announced the Slackware 1.00 release that was inspired by the Softlanding Linux System…
10 Tips to Avoid Sweating About IT This Summer
Here are guidelines on how to keep cool this summer when it comes to IT. These tips range from backing up data to cross-training staff.
OSCON 2014 – The Art of Tizen UI Theme Technology in Various Profiles
Tizen, the follow on Operating System (OS) from MeeGo, is aimed at various profiles, not only mobile, just like MeeGo was. With that in mind a User Interface (UI) must be scalable and themeable to support these diverse profiles. Daniel Juyung Seo, who is a software engineer from Samsung, will be presenting at OSCON at 11:30am 23rd July a session entitled “The Art of Tizen UI Theme Technology in Various Profilesâ€. There will also be a stand at OSCON with demonstrations about the Tizen SDK. The presentation will share the technology behind the scalable and themeable Tizen UI which is called EFL (Enlightenment Foundation Libraries). With some configuration, you can reuse the same UI elements in different sized devices easily, regardless of DPI. This will reduce development time tremendously to support multiple products and applications. A couple of devices are already being shipped based on this technology. If you are attending OSCON, please make sure you check out Daniel’s session at 11:30am on the 23rd July, and also the Tizen SDK demos.
The post OSCON 2014 – The Art of Tizen UI Theme Technology in Various Profiles appeared first on Tizen Experts.
Heterogeneous Multicore Dev Platform Targets Linux
Mentor Graphics has released a heterogeneous multicore development platform for combining Linux, Nucleus, and bare metal OSes on a single multicore SoC. Just as Wind River had its VxWorks real-time operating system before it developed its embedded Linux distribution, Mentor was known for its Nucleus RTOS years before it acquired embedded Linux experts Embedded Alley […]
Linux System Administration Skills are Changing
 When was the last time you compiled a kernel? For many of the latest generation of Linux admins, the answer is really simple: never. I am one of those, provided we don’t count a few times I tried it just for fun, then couldn’t see why I would need a custom kernel and went back to my out-of-the-box kernel.
When was the last time you compiled a kernel? For many of the latest generation of Linux admins, the answer is really simple: never. I am one of those, provided we don’t count a few times I tried it just for fun, then couldn’t see why I would need a custom kernel and went back to my out-of-the-box kernel.
SysAdmin skills move up the stack
Faults in Linux 2.6
Six researchers (including Julia Lawall of the Coccinelle project) have just released a paper [PDF] (abstract) that looks at the faults in the 2.6 kernel. “In August 2011, Linux entered its third decade. Ten years before, Chou et al. published a study of faults found by applying a static analyzer to Linux versions 1.0 through 2.4.1. A major result of their work was that the drivers directory contained up to 7 times more of certain kinds of faults than other directories. This result inspired numerous efforts on improving the reliability of driver code.
“Today, Linux is used in a wider range of environments, provides a wider range of services, and has adopted a new development and release model. What has been the impact of these changes on code quality? To answer this question, we have transported Chou et al.’s experiments to all versions of Linux 2.6; released between 2003 and 2011. We find that Linux has more than doubled in size during this period, but the number of faults per line of code has been decreasing. Moreover, the fault rate of drivers is now below that of other directories, such as arch. These results can guide further development and research efforts for the decade to come. To allow updating these results as Linux evolves, we define our experimental protocol and make our checkers available.” (Thanks to Asger Alstrup Palm.)
Fedora 21 Starts Working Towards Its Alpha Release
In aiming towards an on-time release of Fedora 21, developers have spun the first test candidate for the upcoming development release…
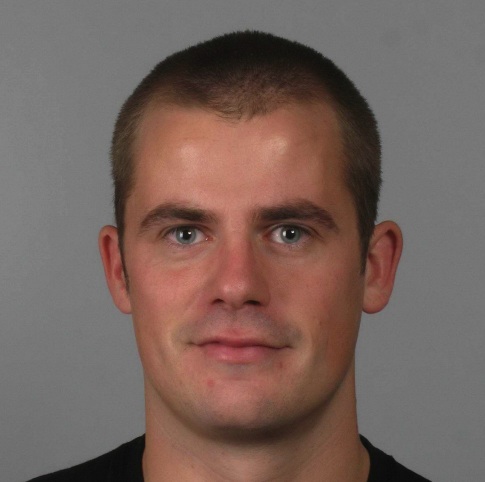
Linux Foundation SysAdmin Konstantin Ryabitsev, an SELinux Expert
This is the fourth profile in a series on Linux Foundation system administrators leading up to SysAdmin Day. Do you have a super-hero sysadmin you’d like to recognize? Send your nomination to This e-mail address is being protected from spambots. You need JavaScript enabled to view it
by July 25 and enter them to win a free ticket to LinuxCon and CloudOpen North America taking place in Chicago August 20-22, 2014. (See the full contest announcement for more details.)
 Konstantin Ryabitsev is a system administrator on the Linux Foundation’s Collaborative Projects IT team. Here he discusses why he became interested in IT security, his approach to working with developers, and his love of human languages, among other things. (Also, see our May 2013 article on what it’s like to be a Linux Foundation sysadmin, starring Konstantin.)
Konstantin Ryabitsev is a system administrator on the Linux Foundation’s Collaborative Projects IT team. Here he discusses why he became interested in IT security, his approach to working with developers, and his love of human languages, among other things. (Also, see our May 2013 article on what it’s like to be a Linux Foundation sysadmin, starring Konstantin.)
Linux.com: How long have you been a sys admin?
I set up my very first Linux system in 1998. It was a combination web server and mail server running on an old beige tower and served the non-profit where I worked at the time extremely well. I didn’t know enough about systems administration at the time to keep sendmail patched, so six months later the system was also serving “warez.” Needless to say, that catapulted IT security to the forefront of my interests.
When did you start at the Linux Foundation and how did you get the job?
I started in November 2011. I was working at McGill University InfoSec at the time, and was also active with Fedora Project — which is how my name showed up on the list of candidates. The Linux Foundation was looking for a systems administrator with a strong background in IT security — who would also be a good fit for a decentralized team of passionate open-source advocates. I’m extremely glad I was a good fit for the position, as I can’t imagine receiving as much satisfaction from any other job.
What do you do for the Linux Foundation? What’s your specialty?
I’m part of the Collaborative Projects IT team, which is responsible for providing IT hosting for projects like kernel.org, codeaurora.org, opendaylight.org, allseenalliance.org, and a few others. The requirements are different for each project, so our specialty is working with the developers involved in each one of them and finding solutions that would satisfy their needs. We provide a full development stack, from git repository hosting to continuous integration and release distribution. We try not to specialize in any one thing, but we
certainly have areas where each member of the team has higher expertise than others. I am usually the go-to resource for SELinux policies and other process confinement questions.
Will you describe a typical day at work for you?
We are very client-oriented, so we try to give priority to incoming developer requests. We try to automate as much as we can, but a lot of things still require admin involvement, especially with regards to continuous integration (CI) systems. Besides that, there’s always documentation to be written or updated, or some system refactoring to do. We’ve added a number of very large projects in a very short period of time throughout the last 18 months, so some of the decisions we’ve made along the way require rethinking in order to allow us to scale better. Unfortunately, once you have production systems in place, refactoring requires very careful planning — otherwise you risk downtime that would interfere with project timelines.
What’s your favorite part of the job/ thing to do and why?
Every sysadmin’s guilty pleasure is writing a tool that would automate away a menial task. I call it “guilty pleasure” because sometimes the total amount of effort spent on writing such tools goes vastly beyond what it would take to continue doing things manually (obligatory xkcd link: http://xkcd.com/1205/). However, sysadmins hate being distracted by small requests (we have “the zone,” too, just like programmers: http://heeris.id.au/2013/this-is-why-you-shouldnt-interrupt-a-programmer/), which is how we justify our efforts. Thankfully, we don’t have to justify them to management — only to fellow members of the sysadmin team.
What is your nightmare scenario? How have you prepared for it?
Well, if we’re prepared for it, then it’s no longer the nightmare scenario. 🙂 We try to introduce lots of redundancy into the infrastructure to assure that there are as few single points of failure as possible, but at some point you have to do risk-benefit analysis and draw the line past which such redundancy becomes prohibitively expensive either in terms of money or effort. For example, if there’s a major natural calamity on the North American West coast, we’ll definitely be impacted, since most of our infrastructure is in Portland, Oregon.
However, we will be able to recover without any data loss due to off-site backups in Montreal. A more realistic nightmare scenario would be a systems failure while the sysadmins responsible for that particular part of the infrastructure are not reachable, which is why we try to keep ample documentation. Oh, and the rule is that we don’t all fly to Linux Foundation events on the same days, so as not to all be in the air at the same time. 🙂
What is your favorite sysadmin tool and how do you use it?
I don’t really have a favorite tool — not any more than a plumber would have a favorite wrench (yes, I think plumbers are a great analogy for sysadmins). I do have a preferred set of tools that I use every day, but I expect it’s similar to what most other sysadmins keep in their proverbial tool belt.

What’s your favorite story about working at the Linux Foundation?
The thought that we are in a position to tell Linus what he can and cannot do on the Linux systems we manage makes me giggle every time – because it’s so wonderfully absurd. However, I would say my favorite bit is how many companies are so eager to help you out if they find out that you are working for the Linux Foundation. We rely on the goodness of a great number of donors to run our infrastructure — most of whom volunteered their services without any prompting on our part. My thanks go out to Google, Rackspace, ISC, Intel, Vexxhost, Yubico — among many others — for helping us with hardware and hosting. And, of course, to all the generous members of the Linux Foundation. You make it possible for us to run infrastructure where Linux development itself happens.
What do you do for fun, in your spare time?
I’m a (human) language nerd, so my favorite hobby is learning how to read books over and over again in different languages. It’s like crossword puzzles on a nightmare level. I can read fluently in four languages (English, Russian, French, and Spanish.) When I don’t have spare brain cells left, though, I enjoy walking, biking, and being generally silly with my family.
Read more about Linux Foundation System Administrators:
Linux Foundation SysAdmin Michael Halstead’s IT Career Started at Age 15
Linux Foundation SysAdmin Andy Grimberg Loves New Tech and Snowboarding
To Linux Foundation SysAdmin Ryan Day, Elegance is the Best Tool
Chromecast Now Lets Users Move Android Content to Their TVs
Google’s $35 Chromecast dongle can now push Android content from small devices to the television screen.
How Russian Hackers Stole the Nasdaq
In October 2010, a Federal Bureau of Investigation system monitoring U.S. Internet traffic picked up an alert. The signal was coming from Nasdaq (NDAQ). It looked like malware had snuck into the company’s central servers. There were indications that the intruder was not a kid somewhere, but the intelligence agency of another country. More troubling still: When the U.S. experts got a better look at the malware, they realized it was attack code, designed to cause damage.
As much as hacking has become a daily irritant, much more of it crosses watch-center monitors out of sight from the public. The Chinese, the French, the Israelis—and many less well known or understood players—all hack in one way or another. They steal missile plans, chemical formulas, power-plant pipeline schematics, and economic data. That’s espionage; attack code is a military strike. There are only a few recorded deployments, the most famous being the Stuxnet worm. Widely believed to be a joint project of the U.S. and Israel, Stuxnet temporarily disabled Iran’s uranium-processing facility at Natanz in 2010. It switched off safety mechanisms, causing the centrifuges at the heart of a refinery to spin out of control. Two years later, Iran destroyed two-thirds of Saudi Aramco’s computer network with a relatively unsophisticated but fast-spreading “wiper†virus. One veteran U.S. official says that when it came to a digital weapon planted in a critical system inside the U.S., he’s seen it only once—in Nasdaq.
Read more at Bloomberg Businessweek.
