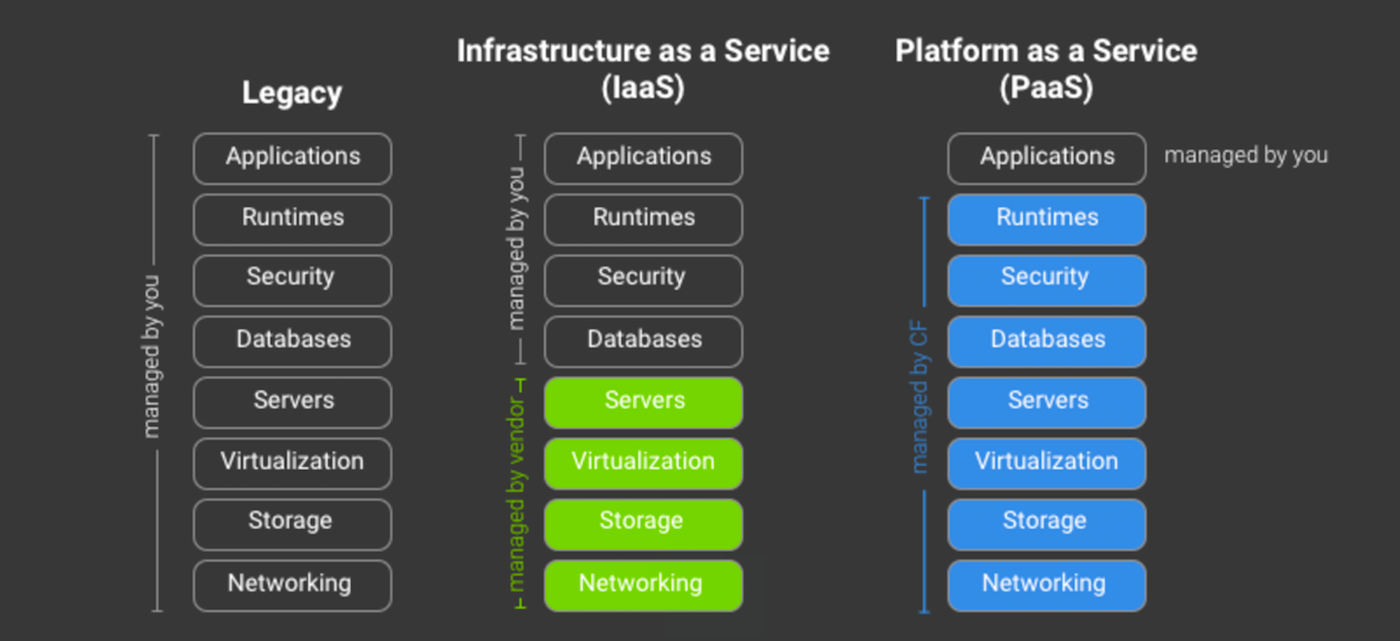
You’ve heard about Cloud Foundry, and you know it’s growing fast and might be something you’re interested in. But what exactly is Cloud Foundry? One possible short answer is Yet Another Cloudy Thingy, because there sure are a lot of cloud projects. A better short answer is Platform as a Service (Paas), for building, managing, and deploying cloud-native applications.
In this series, you will learn about Cloud Foundry and how to get started using it to develop applications. In the first three blogs, we’ll cover basic concepts, terminology, a technical overview and architecture, and in the last two blogs we’ll learn how to write and push an app to a Cloud Foundry instance. The information in this series is based on the Cloud Foundry for Developers (LFD232) training course from Cloud Foundry and The Linux Foundation. You can download a sample chapter from the course here.
What is PaaS?
The goal is to streamline application development and management by relieving developers from the hassle of building and maintaining their own development and deployment environments. A PaaS host looks the same to the user, whether it is local or remote: all you need is computer and a network connection to access everything you need.
Cloud Foundry
There is a ton of information on cloudfoundry.org, but you have to dig to find out what Cloud Foundry is. It is a platform for building PaaS projects; it is not a standalone product but must run on top of an IaaS (Infrastructure as a Service) platform. Cloud Foundry was created at VMware in 2009 and was designed to run on VMware vSphere.
Cloud Foundry morphed and grew until it was spun off as an independent non-profit Linux Foundation project. It uses Open Container Initiative and lot of other cloud technologies including Docker, Kubernetes, and BOSH. Cloud Foundry also runs on OpenStack and aims to be platform-neutral, running on any IaaS. If you want to try building your own Cloud Foundry instance, follow these instructions on OpenStack.org. If you want to jump right into application development and not hassle with building your own PaaS, CloudFoundry.org maintains a list of certified providers, where you can get started for free or low-cost.
The Foundation certifies these projects, which must meet certain standards. The Cloud Foundry license is the Apache License 2.0, a permissive license that allows releasing modified code under different licenses, and grants permissive patent rights. The Foundation also offers developer certifications, and administers the Cloud Foundry Certified Developer Exam.
The Cloud Foundry Foundation owns the trademarks and manages the project, which is not a small task, as contributors and supporters include some industry heavyweights. The Foundation’s job is to be neutral and ensure that no single entity can control the code. There are a host of “intellectual property” (I loathe the term, but we’re stuck with it) issues to navigate and harmonize. If this sort of thing interests you, visit Cloud Foundry Foundation to learn all about governance, their board of directors, membership, and a host of other tasks and issues that the Foundation manages.
“Every Business is a Software Business”
This is a popular quotation now, and while I don’t agree completely with it, it is true that most businesses must be tech-savvy about custom app development. Cornelia Davis of Pivotal says: “You are either building a software business, or losing to someone who is.” Some classic examples are Netflix vs. Blockbuster, Uber and Lyft vs. cab and limo companies, Airbnb vs. the hotel/motel industry.
Not everyone is entirely happy with this invasion of software into everything. Every restaurant, store, and product now has its own app, and more and more devices want to yap at us all the time. Remember Ray Bradbury’s short story “The Murderer”? Albert Brock is fed up with the incessant din of modern society, people calling him on his wrist radio, and even his house nags him, so he embarks on a crusade of destruction to shut everything up. Quite prescient for 1953.
But, this is the state of our world now, and this is where the growth and opportunities are for software developers. And, to keep up with these modern times, over the next four parts of this series, you’ll learn how to get started with using Cloud Foundry as your development platform. Join me as we get started learning and building.
Download the Cloud Foundry for Developers sample chapter now.