It’s been two years since the open source RISC-V architecture emerged from computer labs at UC Berkeley and elsewhere and began appearing in soft-core implementations designed for FPGAs, and over a year since the first commercial silicon arrived. So far, the focus has primarily been on MCU-like processors, but last October, SiFive announced the first Linux-driven RISC-V SoC with its quad-core, 64-bit Freedom U540 (AKA U54-MC Coreplex). A few days ago at FOSDEM, SiFive opened pre-sales for an open source HiFive Unleashed SBC that showcases the U540.
The $999 HiFive Unleashed is available on Crowd Supply, with shipments due on June 30. The 28nm fabricated U540 SoC that drives the SBC is not only the first multi-core and Linux-ready RISC-V processor, but the first to provide cache coherence. In addition to the four 1.5GHz U54 RV64GC CPU cores, the SoC includes an E51 RV64IMAC management core with Sv39 virtual memory support.
Each CPU core provides a five-stage in-order pipeline, along with 32KB L1 instruction and data caches, and there’s also a shared, coherent 2MB L2 cache. Because both the L1 instruction and L2 caches can be configured into high-speed deterministic SRAMs, the SoC can be used for real-time applications.
What you won’t find is a GPU or VPU. However, third parties are encouraged to integrate them. Silicon developers can tap an open source TileLink interface bus to build peripheral IP. The TileLink bus’ scalable cache-coherent fabric is further enabled with bridge adapters for legacy bus protocols such as AXI4, AHB-Lite, and APB.
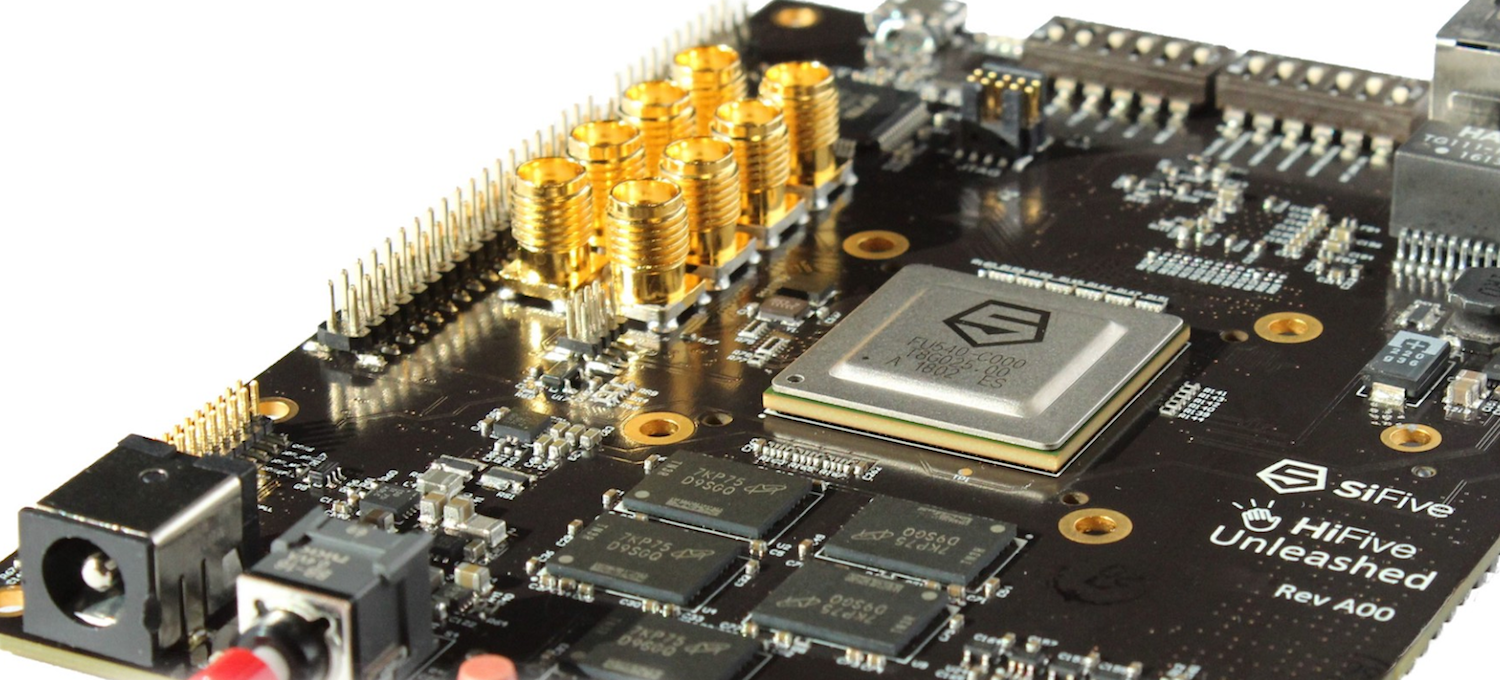
The open spec HiFive Unleashed board integrates a U540 SoC, 8GB of DDR4 RAM, and 32MB quad SPI flash. The only other major features include a microSD slot, a Gigabit Ethernet port, and an FMC connector for future expansion. A SiFive rep confirmed to Linux.com that the board will be open source hardware, with freely available schematics and layout files.
The feature set may be pretty limited for $999, but you’re really paying for the novel SoC and a chance the get a head start on what could potentially become a major new computing platform.
RISC-V jumps out to a fast start
It’s too early to say whether RISC-V will ever rival ARM or x86, let alone match the reach of fading architectures such as MIPS and PowerPC. So far, however, there has been a surprising willingness on the part of major computer and semiconductor vendors to experiment with the new ISA. RISC-V Foundation Platinum members include heavy hitters like Draper, Google, Hewlett Packard Enterprise, IBM, Microsemi, Oracle, Microsoft, Nvidia, and Qualcomm.
The widespread interest is partially due the fact that RISC-V has a free and permissive license that enables third parties to use the ISA to develop proprietary implementations. The expectation, however, is that most RISC-V SoCs will follow the early players’ leads in providing open source implementations.
RISC-V’s timing seems to be right, as the growing acceptance of open source software and hardware logically leads to a desire to open up of the processor. Opaque chip designs often create obstacles and blind spots — not only for open source projects, but also semiconductor vendors. Conceivably, hidden issues such as Intel’s Spectre and Meltdown security problems might have come to light more quickly in the open source spotlight.
There’s also a sense that the dominance of two closed source architectures — ARM and Intel x86 — is limiting innovation, slowing time to market, and increasing cost. In addition, RISC-V advocates claim that both ARM and x86 platforms are burdened by legacy code. By comparison, RISC-V is starting with a clean slate of modern components.
SiFive was founded by RISC-V inventors including Yunsup Lee, Andrew Waterman, and Krste Asanovic, based in part on two earlier open source RISC ISAs: SPARC and OpenRISC. In 2014, Asanovic and fellow UC Berkeley professor David Patterson, who coined the term RISC, posted a white paper on RISC-V, and development progressed rapidly from there.
SiFive has been the major RISC-V hardware player, while Microsemi has led the way in developing soft-core implementations that can run on FPGAs for prototyping. In Nov. 2016, SiFive announced an open source, Arduino compatible HiFive1 development board for its Freedom E300 — an MCU-like RISC-V design with an E31 Coreplex core designed to run FreeRTOS. Developers could also use Microsemi’s soft-core SmartFusion 2 SoC FPGA to develop for the E300.
The HiFive1 was followed last May by an Arduino Cinque board based on the HiFive1, jointly developed by SiFive and Arduino. The key addition was an Espressif ESP32 SoC that supplies WiFi and Bluetooth.
SiFive and Microsemi aren’t the only vendors invested in RISC-V. Andes, Bluespec, Codasip, and Cortus sell RISC-V core IP that can be used to develop MCU-like SoCs. (SiFive also sells IP in addition to silicon and development services.) Like Microsemi, Rumble and Development and VectorBlox offer soft cores that run on FPGAs.
According to a recent summary of RISC-V developments posted on Electronic Design by Microsemi’s Ted Marena, Vice Chair of the RISC-V Foundation’s RISC-V Marketing Committee, software support is also evolving. In the Linux realm, RISC-V support was added to the GNU/GCC and GNU/GDB toolchains last May. In addition, writes Marena, “several flavors of Linux are supported, including Yocto,” based on Linux 4.6. RISC-V support appears to be headed for a merge into kernel 4.14, which “means RISC-V will soon be a mainline platform in Linux.”
The HiFive Unleashed Crowd Supply page does not have much to say about software aside from noting Linux compatibility, and SiFive did not respond to our queries for more details. When the U540 SoC was announced, however, SiFive said the SoC would be supported by “a rich SDK with demo software and an easy-to-install binary toolchain.” Standard development and debug tools such as OpenOCD, GDB, and an Eclipse IDE, were also said to be in the works.
Performance questions should be partially answered when the HiFive Unleashed appears this Spring. According to an EETimes story posted in October, the “single issue” U54 core is expected to lag the performance of the “dual issue” Cortex-A53. Marena, however, claims that “the modularity of the RISC-V ISA design enables implementations to be more efficient than legacy ISAs such as x86 or ARM.”
In conjunction with the Embedded Linux Conference + OpenIoT event to be held in Portland, Oregon on Mar. 12-14, SiFive will host the first hackathon for the HiFive Unleashed. Registered SiFive Developers will be able to attend the Portland event to try out the SBC. (More information may be found on the HiFive Unleashed product page.) The ELC conference itself includes a presentation by Comcast’s Khem Raj called OpenEmbedded Yocto on RISC-V — New Kid on the Block.
Registration is now open for the Embedded Linux Conference and OpenIoT Summit, to be held Mar. 12-14 at the Hilton Portland in Portland, OR. Linux.com readers can register now with discount code, LINUXRD5, for 5% off the attendee registration.