If you’re seriously concerned about privacy, you want to ensure you’re doing all the right things and not leaving behind a trace of what you’ve browsed. There are many reasons for this—some good, some bad. I’d like to focus on the good (naturally). In the past few years, it has become clear that tracking web histories is not a myth. Businesses, governments—anyone with the skills can make use of your browsing history. That is the very reason why technology like Tor has recently gained popularity.
Users want to reclaim their anonymity.
That is where the likes of Tails comes in. Tails lays claim to “Privacy for anyone” and they make good on that claim with tools like:
-
Tor — Tails relies on the Tor anonymity network
-
Tor Browser — A browser that works seamlessly with Tor
-
Onion Circuits — A tool that lists the circuits used by Tor
-
OnionShare — Anonymously share files
By using all of the above, on top of a live-only distribution, Tails makes for a very anonymous experience. And because it all works together seamlessly, you don’t have to worry about certain dependent components (e.g., starting Tor before using Tor Browser). In fact, you can fire up Tails, open up Tor Browser and immediately go to the Tor Check site and see that your Tails instance is, in fact, configured to use Tor.
This is privacy at it simplest—with a slight catch.
But wait; what exactly is Tails?
As I mentioned earlier, Tails is a live Linux distribution. What does that mean? It means you don’t install the operating system, you run it on a per-instance basis, use it for as long as you need, and shut it down when you’re done. If you want to use Tails, you burn the ISO (you must use either Firefox or Tor Browser, to download the ISO) onto a USB drive, stick the USB drive into your machine, and boot. Enjoy the privacy of Tails and then, when you’re done, reboot the computer (removing the USB drive). Everything you did within Tails is gone; you have left absolutely no trace. And, if you work with the likes of VirtualBox, you can create a virtual machine with the ISO and have Tails at the ready any time (just remember to shut it down and not save the VM in its running state).
And so, for anyone that is looking to gain as much privacy as they can, Tails is one of the easiest solutions.
What’s new in Tails 3?
Startup and shutdown
Tails 3 brings about some significant changes to the platform. First and foremost, there’s a brand new startup and shutdown experience. When you boot Tails 3, the first thing you will see is the Tails Greeter (Figure 1). In this screen, you can select your Language, Keyboard Layout, and Date/Time formats.
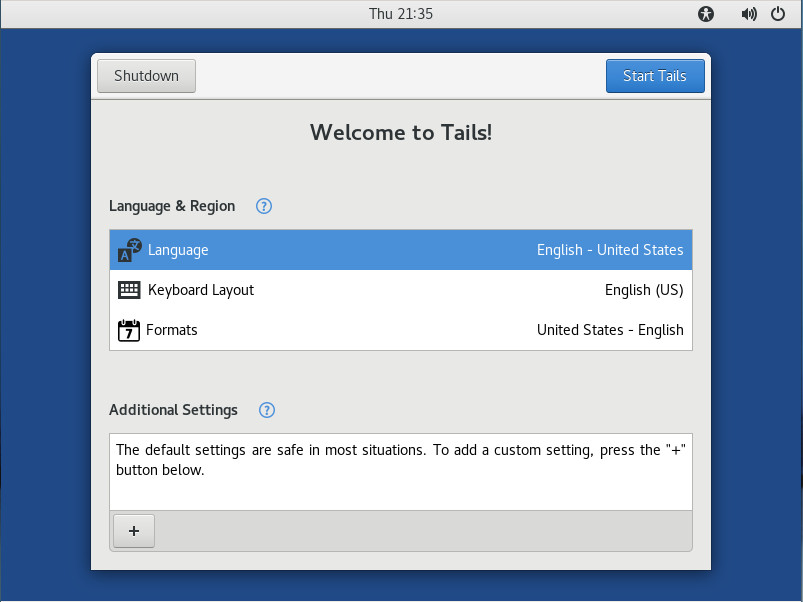
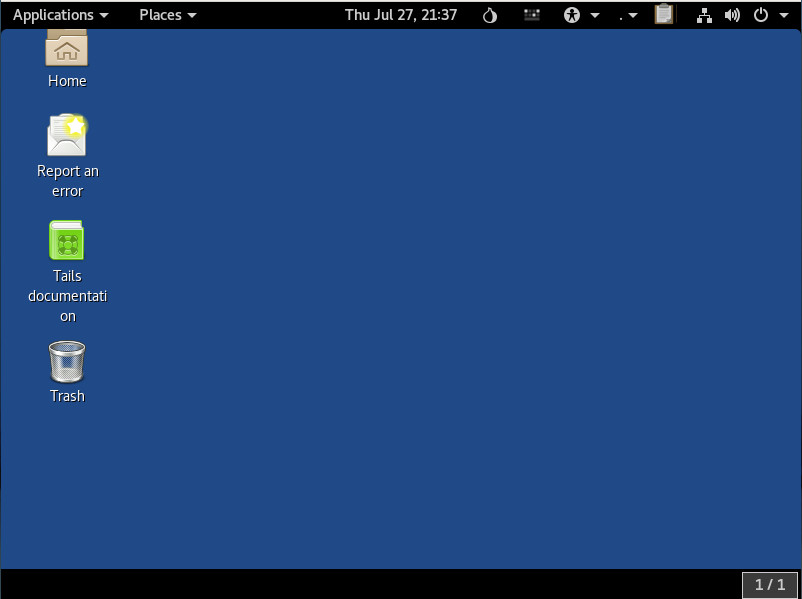
Click on Additional settings and you can configure an administrator password (which is off by default), MAC address spoofing (on by default), and Network Connection (direct by default). Once you’ve configured Tails how you want it, click the Start Tails button and the default desktop will appear (Figure 2).
The improved desktop
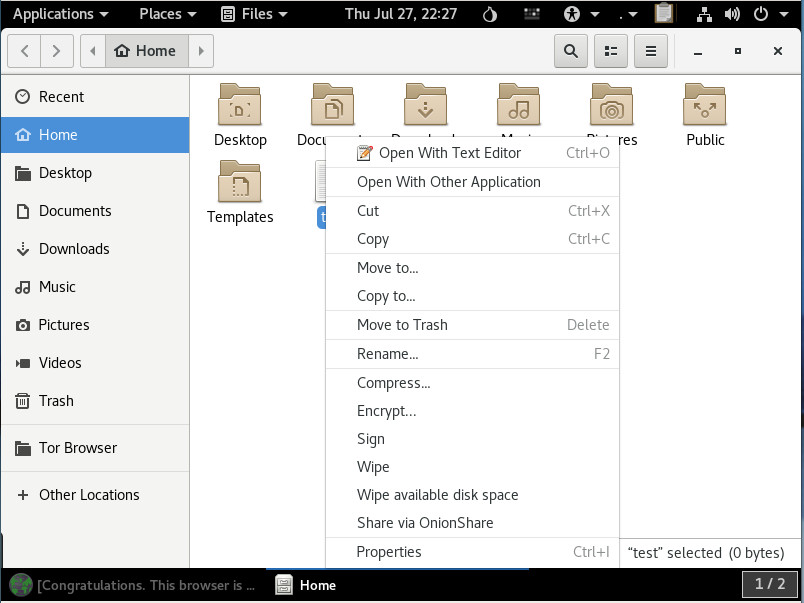
The desktop is based on GNOME (with a slight tweak or two, by way of extensions) and is quite user-friendly. One of the first things previous users will note is that Tails has opted to go to the dark side, using the darker GNOME theme as the default. Speaking of the desktop, the Tails file manager (GNOME Files) finally includes the built-in ability to compress and extract as well the ability to rename multiple files at the same time. Add to that, Tails makes it easy (by way of GNOME Files) to encrypt, sign, wipe, and share (via OnionShare) files, through a right-click context menu (Figure 3).
No more 32-bit support
That’s right, Tails has opted to leave behind the aging 32-bit hardware support. This was a tough decision on their part, but it was the right move, as there is more security to be found within the 64-bit architecture.
Software updates
A number of the software packages have enjoyed updates. Once you boot up Tails, you’ll find the following release changes:
-
KeePassX from 0.4.3 to 2.0.3
-
LibreOffice from 4.3.3 to 5.2.6
-
Inkscape from 0.48.5 to 0.92.1
-
Audacity from 2.0.6 to 2.1.2
-
Enigmail from 1.8.2 to 1.9.6
-
MAT from 0.5.2 to 0.6.1
-
Dasher from 4.11 to 5.0
-
git from 2.1.4 to 2.11.0
As you can see, many of those titles are nowhere near bleeding edge; but when you’re using a live distribution, such as Tails, you’re not concerned with having the newest of the new. Even so, just because you’re looking for anonymity, doesn’t mean you don’t need to get things done. Tails has plenty of software to help you do just that. You’ll even find titles such as:
-
GIMP
-
Inkscape
-
Scribus
-
Thunderbird
-
Pidgin
-
Pitivi
-
Sound Recorder
-
And much more
In other words, don’t be fooled by the fact that Tails is a live distribution; this is still Linux, so there’s plenty of software to be had.
To read about all the changes that have been made to Tails, check out their official post here.
Amnesia
One thing you should know about tails is that it defaults to the user, amnesia. This particular user is not a member of sudo, so it is not allowed to execute tasks that require administrative permission. You can get around that during the startup. Click Additional settings at the Tails Greeter and then click Administration password. Type and verify the new administrator password and click Add (Figure 4).
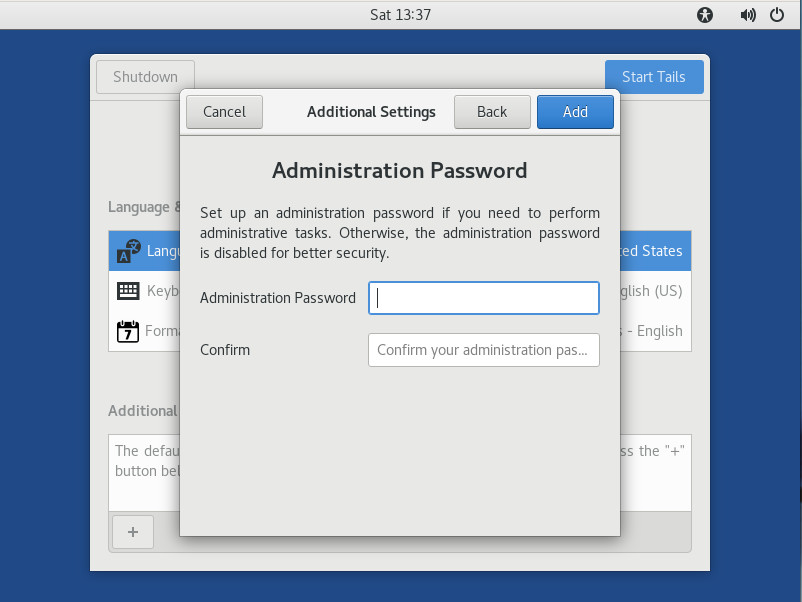
Once you’ve started Tails with an administrator password in place, the amnesia user can then work with tools like sudo. Do note, as soon as you restart Tails, that administrator password is gone and will have to be reset.
Is Tails right for you?
This question is fairly easily answered. Are you looking for the means by which you can browse and work anonymously, knowing once you shut down every trace of what you were doing will vanish? If that’s you, Tails might well be the perfect fit. Give Tails 3 a spin and enjoy anonymity at its simplest.
Learn more about Linux through the free “Introduction to Linux” course from The Linux Foundation and edX.