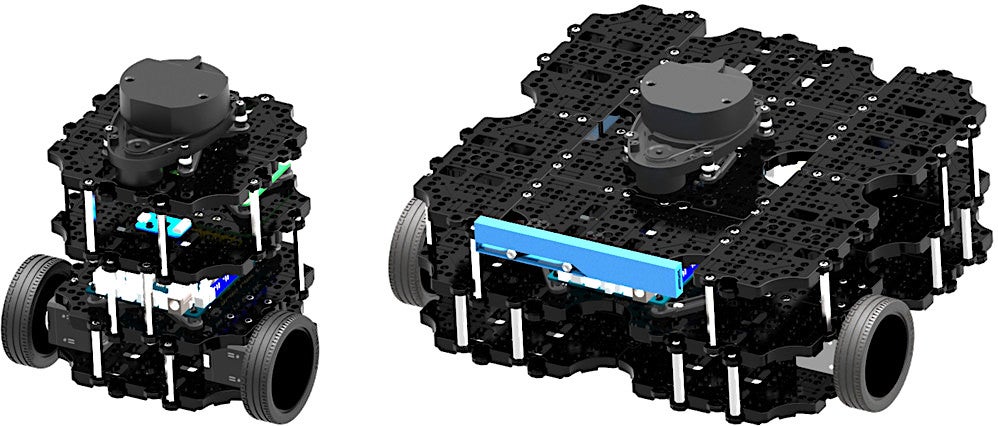
The TurtleBot 2, which Open Robotics calls the “world’s most popular open source robot for education and research,” has long been the de facto development platform for the open source Robot Operating System (ROS). Many TurtleBot developers run ROS from Ubuntu, but Windows is also available on the netbook “brain” nestled inside the two-wheeled bot. The newly shipping TurtleBot 3 replaces the Intel Core based netbook with a choice of two embedded Linux computers running Ubuntu with ROS: the TurtleBot 3 Burger runs Ubuntu on a Raspberry Pi 3 while the larger TurtleBot 3 Waffle instead integrates a more powerful, Atom-based Intel Joule computer-on-module.
The Robotis-built TurtleBot3 is smaller, cheaper, simpler, and more powerful than the TurtleBot 2. The kit design is also “the most affordable robot among the SLAM-able mobile robots equipped with a general 360-degree LiDAR,” says Open Robotics, a subsidiary of Open Source Robotics Foundation (OSRF), which first developed ROS.
SLAM (simultaneous localization and mapping) algorithms work with laser-based LiDAR and other depth-imaging systems to help the robot map an unknown environment while keeping track of its position within it. Both the $549 Burger and the $1,799 Waffle integrate 360-degree HLS-LFCD LDS LiDAR systems, thereby enabling autonomous navigation. The Waffle also provides Intel’s RealSense depth-finding camera as an alternative to LiDAR.
The Raspberry Pi or Intel Joule boards work together with a fully open source OpenCR control board built by Robotis that runs Arduino IDE code on a Cortex-M7 STM32F7 MCU. The board controls sensors including a built-in IMU and optional touch, IR, color, and other sensors. It also controls one of the other major innovations on the TurtleBot 3: the integration of high-end Robotis Dynamixel actuators.
Located in the TurtleBot’s two sprocket wheel joints, the Dyamixels provide velocity control for the wheels, as well as torque or position control for the joints. The Burger’s Dynamixel XL420 supports four operating modes while the Waffle’s Dynamixel XM430 supports six modes, providing even greater flexibility.
The TurtleBot3 is equipped with an 1800mAh battery, and can be remotely operated with a variety of wireless devices, including keyboards, gaming joysticks, and the LEAP Motion controller. The design is highly modular, and Robotis sells optional sensor and chassis components, as well as a variety of Robotis arms and grippers.
Between the Raspberry Pi and Joule on the one hand and the I/O studded OpenCR control board on the other, there should be plenty of opportunities for hardware hacking with different cameras, sensors, and other gizmos. The TurtleBot3 design ships with 3D CAD files for mechanical parts, as well as schematics, PCB Gerber, and BOM for the OpenCR board.
Although the TurtleBot 3 defaults to Ubuntu 16.04.2 with ROS Kinetic, you can likely use any ROS-compatible Linux distro that runs on the Raspberry Pi or Intel Joule. An Ubuntu Insights announcement of the robot noted that both the Pi and Joule support Ubuntu Core. Conceivably, experienced hackers could also swap out the Pi and Joule for another embedded Linux computer that supports ROS.
Other Pi- and Linux-Based Robots
Most robots that run on the Raspberry Pi are less sophisticated devices that lack LiDAR, such as the mobile GoPiGo and Piborg’s six-wheeled DiddyBorg. Other choices include the open source, Raspberry Pi and Arduino-based FarmBot Genesis farming robot. Some additional Pi-based kits are summarized here, but there are many more designs posted online.
A variety of higher end robots integrate other embedded Linux boards, such as the ambulatory, humanoid Poppy Humanoid, which runs Ubuntu 14.04 on an Odroid XU4. The most famous tuxified humanoid bot these days is the Softbank/Aldeberan Pepper hospitality robot. Linux robots have also entered the industrial space with models like Rethink’s Sawyer manipulation bot.
More information on the TurtleBot 3 may be found in this LinuxGizmos post and IEEE Spectrum hands-on story, as well as the TurtleBot3 shopping page and TurtleBot community site.
Connect with the Linux community at Open Source Summit North America on September 11-13. Linux.com readers can register now with the discount code, LINUXRD5, for 5% off the all-access attendee registration price. Register now to save over $300!