It is often faster to use command-line apps to play audio files and preview images than to futz around launching and using a graphical application, and you can use them in scripts. Come along to learn about MOC and SoX for playing audio files, and feh for viewing image files from the Linux command line.
MOC, Music on Console
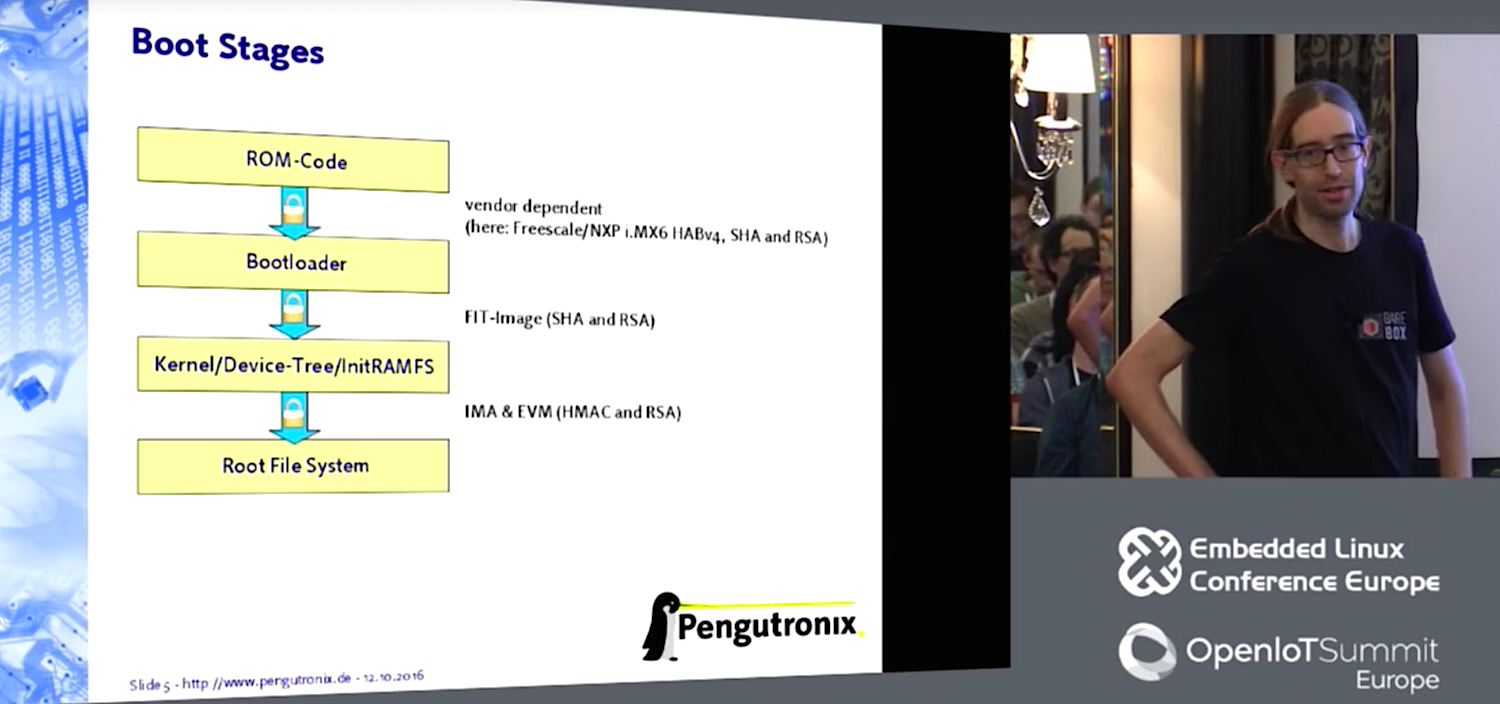
MOC plays audio files from an X terminal, and from a console with no X windows, such as a headless server with no graphical environment. MOC supports most audio file formats including OGG, WAV, FLAC, MIDI, MP4, and MP3. Note that the correct command is mocp and not moc. moc is a Qt command, the Meta Object Compiler, so if you run it you’ll get a “No relevant classes found” error. The simplest use is to start it and name a directory that contains audio files:
$ mocp sounds/ambient/
You’ll see something like Figure 1, a nice Midnight Commander-style two-pane file manager where you can navigate all over your filesystem and find audio files to play. Figure 1 has a playlist in the right pane; add files from the left pane to your playlist by highlighting them and pressing the a key. Press V to save your playlist in the current directory.
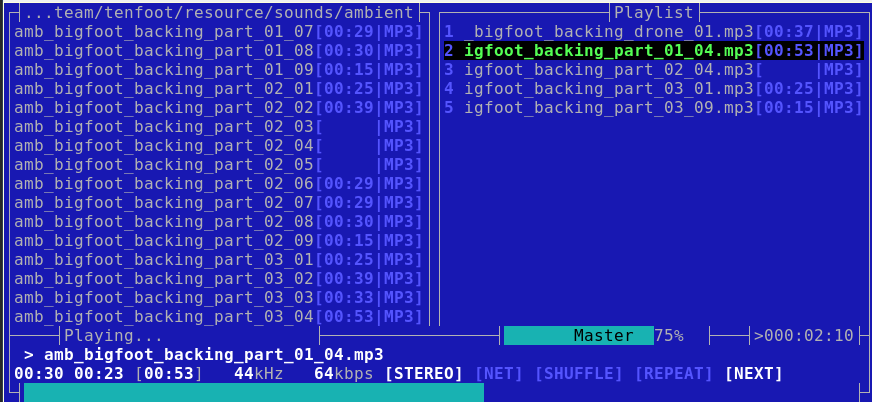
By default MOC plays all the files in the current directory. Use the Tab key to toggle between the file list and your playlist. Navigate up and down with the arrow keys, and press Enter to select a file to play. These are the basic commands, and note that they are case-sensitive:
- < and > control the volume level
por spacebar toggle pause/playnplays the next file,bplays the previous fileStoggles shuffle- Right arrow key seeks forward and Left arrow key seeks backward
qdetaches from the MOC interface and returns to your prompt, and your audio keeps playingmocpreturns to the MOC interface from your command lineQfrom the MOC interface quits MOCmocp -xfrom any command prompt closes MOC
MOC commands are different in the MOC interface than on your command line. man moc details the commands that you run on the command line, and press h to see a list of commands in the MOC interface.
Your personal MOC directory is ~/.moc. The example configuration file is in /usr/share/doc/moc/examples/config.example.gz. You can extract and copy this example file to ~/.moc/config, or just copy the bits you want to use. I use the MusicDir option to set my default playlist, and you may set a default directory instead. List your audio directories in the Fastdir options for fast switching:
MusicDir = /home/carla/.moc/list2.m3u Fastdir1 = /home/carla/tutorials Fastdir2 = /home/carla/sessions Fastdir3 = /home/carla/music-for-dull-meetings
Start MOC in your MusicDir with mocp -m, or press m in the MOC interface.
Press Shift+1, Shift+2 and so on to change to your various Fastdirs.
MOC has customizable theming and keymaps; see man mocp and the help in the MOC interface to see many more options and controls.
Play One Audio File with SoX
Good old SoX (Sound eXchange) has been around forever and contains a multitude of capabilities. If MOC has an easy way to play just one file I have not found it, so I use SoX for this. This example shows how to play a single file, and shows how to play a file with whitespace in the filename by enclosing it in quotation marks:
$ play "quake2/music/Sonic Mayhem - Quake II/11.ogg"
Just as I do with image files (see the next section), I use locate and grep to find audio files. Then it’s a quick select > middle-click paste to play the file with SoX.
feh X Terminal Image Viewer
I use feh to quickly preview images. You need to be in graphical session, that is, using an X terminal like GNOME Terminal or Konsole. I have over a thousand images on my main PC, and I rely on locate and grep to find what I want. It’s a lot faster to view the image with feh than to open a graphical app and wander through it until I find my my image. Like the photo of my little cat Molly in Figure 2:
$ locate -i molly|grep rock /home/carla/Pictures/molly-on-rocks-small.jpeg $ feh /home/carla/Pictures/molly-on-rocks-small.jpeg

You can also open your images in editors like Inkscape and Gimp this way, for example inkscape /home/carla/Pictures/molly-on-rocks-small.jpeg. In feh, right-click on your image to open a menu full of useful options: rotate, set image as background, delete, image size and type, and several others.
Give feh a directory name to launch a slideshow of all images in the directory, and then click on each image to advance to the next image. feh displays them at their native resolutions, so right-click on any image and check Options > Fullscreen to shrink large images to fit your screen. Or pass in options in your command. This example stops the slideshow after displaying all images once, pauses for four seconds on each image, automatically scales large images to fit your screen, and prints the filename on each image:
$ feh --cycle-once -D 4 --scale-down -d Pictures/2016-april/
Create a montage of all images in a directory with 100-pixel thumbnails:
$ feh --thumbnails --thumb-height 100 --thumb-width 100 --index-info "%nn%wx%h" Pictures/2016-april/
Use the right-click menu to save your montage in your current directory (not your images directory).
Open all images in the directory in their own windows (don’t do this with a large number of images!):
$ feh -w image/directory
You can enter a list of filenames in a text file, one per line, and then pass this list to feh:
$ feh -f mylist
man feh is quite good; it’s well-organized and clear, and details all of feh’s operations which include keyboard shortcuts, mouse shortcuts, and randomizing background images.
Learn more about Linux through the free “Introduction to Linux” course from The Linux Foundation and edX.