If you’ve set up an OpenVPN server to provide secure access to remote workers, you’ve got half the battle won. The next step is to get your users’ (or your) systems ready to connect back to the mothership. Don’t worry, it’s easy to get Linux set up to connect to an OpenVPN server, it just takes a few steps.
Although not as easy as a point and click GUI, the OpenVPN Client is not all that challenging to configure and start up. That will be the primary focus of this article; but, for good measure, we’ll add mention of a few good GUI tools that can also handle the task. For information on how to set up the OpenVPN server, check out the previous installment, “Install and Configure OpenVPN Server on Linux.”
Installation
It is necessary to install OpenVPN on the client. The package to be installed is, as expected, openvpn. To install on Ubuntu, follow these easy steps:
- Open up a terminal window.
-
Run
sudo apt-get install openvpn. - Type the sudo password and hit Enter.
- Accept any dependencies necessary and allow the install to complete.
Believe it or not, that’s it for the installation of OpenVPN.
Configuration of the Client
As discussed in the previous article, there will have been certificates created (on the server) specifically for the client machine. The files that need to be securely copied to the client’s /etc/openvpn directory are:
/etc/openvpn/ca.crt/etc/openvpn/ta.key/etc/openvpn/easy-rsa/keys/hostname.crt(Where hostname is the hostname of the client)./etc/openvpn/easy-rsa/keys/hostname.key(Where hostname is the hostname of the client).
Copy those files over using a tool like scp from the server to the client. If the server doesn’t have direct access to the client, just put them on a flash drive and copy from there.
The first step in the configuration of the client is to copy the sample client configuration file to the proper directory with the command sudo cp /usr/share/doc/openvpn/examples/sample-config-files/client.conf /etc/openvpn. With that file in place, it’s time to make a few edits. Open up /etc/openvpn/client.conf with a text editor (such as Nano or vi) and take a look at the following section:
dev tap
remote vpn.example.com 1194
cert hostname.crt
key hostname.key
tls-auth ta.key 1
Make the changes where:
- vpn.example.com is the address to the OpenVPN server.
- 1194 is the port configured on the OpenVPN server.
- hostname.* is the actual name of the certificate and keyfile names.
Believe it or not, that’s it. The only step that is remaining is to restart OpenVPN with the command sudo /etc/init.d/openvpn restart. Once this service has restarted, the remote LAN should be accessible. Test to make sure by pinging a known address on the LAN behind the VPN.
GUI Tools for Connecting to OpenVPN
Both KDE and GNOME offer plugins for their network manager applets that allow VPN connection to an OpenVPN server. The necessary plugins are:
- KDE: network-manager-openvpn-kde
- GNOME: network-manager-openvpn-gnome
More than likely, those plugins will not be installed on the distribution by default. A quick search using the Add/Remove Software utility will allow for the installation of either plugin. Once installed, the use of the network manager applets is quite simple, just follow these steps (I will demonstrate using the KDE network manager applet):
- Open up the network manager applet by clicking on the network icon in the notification area (aka System Tray.)
- Click on the Manage Connections button.
- Select the VPN tab.
- Click the Add button to open up the VPN type drop-down.
- Select OpenVPN from the list.
- Fill out the necessary information on the OpenVPN tab (Connection Name, Gateway, Connection Type, certificate file locations) See Figure 1 for an illustration of this tab.
- If a static IP address is necessary then set that by selecting Manual from the Method drop-down (in the IP Address tab).
- Click OK to save the settings and dismiss the Connection Settings window.
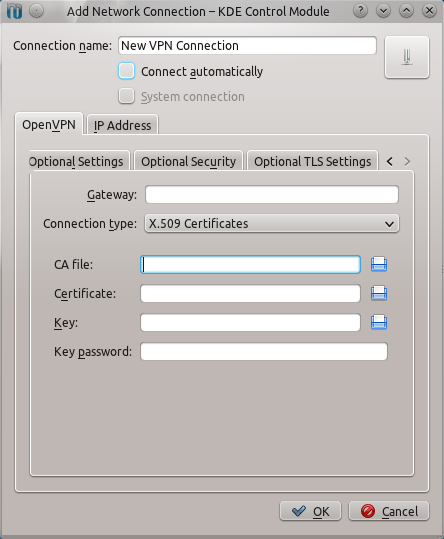 If this client is to always be connected, the Connect Automatically check box can be checked.
If this client is to always be connected, the Connect Automatically check box can be checked.
Now, to connect to the OpenVPN server, using the KDE network manager applet, do the following:
- Click on the network manager applet.
- Click on the Virtual Private Networking button from the popup menu.
- Select the newly created OpenVPN connection.
- Allow the connection to negotiate authentication.
Once the authentication has been negotiated, the VPN connection will be listed as Connected in the network management applet. The VPN LAN should now be accessible.
Gadmin OpenVPN Client
If an alternative desktop is in use, or either KDE or GNOME’s network manager tool doesn’t fit the bill, there is another tool that does a great job of connecting to an OpenVPN server. That tool is Gadmin OpenVPN Client. This tool can easily be installed from within Synaptic, Ubuntu Software Center, PackageKit, and more. Once installed it’s just a matter of firing up the tool (if it can not be found within the menu structure of your desktop, Gadmin OpenVPN Client can be started with the command sudo gadmin-openvpn-client.)
When the tool opens the first thing that needs to be done is the information for the connection must be filled in (see Figure 2).
 Don’t hit the Add button first!
Don’t hit the Add button first!
Make sure to scroll down and fill in all of the necessary information, which includes:
- Connection name: Human readable name for the connection.
- Server address: Address of OpenVPN server.
- Server port: The port configured on the server.
- CA cert/Cert/Key/DH Key/TA key: Location of the certificates generated on the server and then placed on the client. This configuration is all the way at the bottom of the config screen.
After all of this is configured, click the Add button and the connection will then be added. To bring up the connection, select the VPN connection to use and then click the Activate button, which will start the process of certificate negotiation. After the negotiation process is complete, the VPN Network should be available.
As expected, there are plenty of ways to connect to an OpenVPN server. And although not nearly an exhaustive resource (there are more GUI tools to be found in your Add/Remove Software tool), with the above tutorial helping out, a connection can be made from both from the command line and from a GUI. Note that if you’ve got users on Windows and Mac, the OpenVPN folks also have clients for them.





