A firewall can be the single most important tool to manage the security of your Linux machine and network. You can write iptables rules yourself, or find a tool that takes some of the pain out of setting up a firewall. For those that need a strong, but simple solution, and happen to use Ubuntu, there’s Gufw.
I have a mantra with computers: “If a computer is connected to a network, that computer is not safe.” That mantra goes for any computer, no matter the operating system. And although the general consensus is that Linux is a much more secure platform, that does not mean security should be ignored.
Gufw is a very user-friendly way to manage iptables on Ubuntu and can easily allow or block preconfigured services as well as user-specified ports. All of this is handled in a user-friend GUI interface. Gufw also offers incoming traffic reports and logging as well as an easy to manage interface for enabling/disabling a firewall.
Installing Gufw
Just how easy is Gufw to install?
- Open up the Ubuntu Software Center.
- Search for “gufw” (No quotes.)
- Click Install.
Outside of pre-installed, it doesn’t get much easier than that! But, is Gufw just as easy to use as it is to install? Yes. Gufw has been pared down so that it is incredibly simple to use. Gufw only offers the essentials:
- Main window.
- Preferences window.
- Add rule window.
Main Window
From within the Main window (see Figure 1) it is possible to quickly Enable/Disable Gufw, add rules, and view the incoming report.
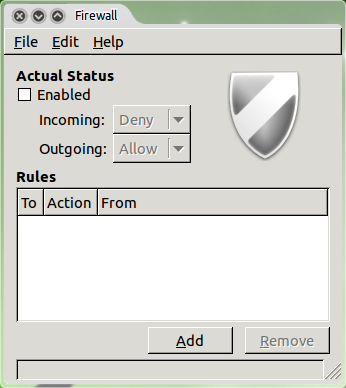 Gufw is one of the simplest firewall tools to use, with a very user-friendly interface.
Gufw is one of the simplest firewall tools to use, with a very user-friendly interface.
Main Window: Enable/Disable
From the main window, to enable or disable the firewall, all that needs to be done is to check (enable) or un-check (disable) the box associated with Enable. Only after the firewall has been enabled, can both the Incoming and Outgoing policies be set. Once enabled, the drop-downs associated with each policy can be selected. The options are:
- Deny: Deny traffic using the Drop target, which silently discards all incoming or outgoing packets.
- Reject: Reject traffic using the Reject target, which sends an error packet to the sender of the incoming packets.
- Allow: Allow incoming or outgoing traffic.
The policy must be set for both Incoming and Outgoing traffic, but both are not required to have the same policy. So Incoming traffic can be set to any of the three options and Outgoing can be set any of the three options. What is set for Incoming and Outgoing will depend on the setup in question as well as the network the machine is on.
Adding Rules
Fortunately, the developers of Gufw allow the creation of user-specific rules. Without the ability to create specific rules, Gufw is of little use outside of the basics. In order to create a specific rule, click the Add button. From this new window (see Figure 2) there are three tabs which allow the creation of rules in different ways:
- Preconfigured: Select from preconfigured rules for specific applications or services.
- Simple: Configure a rule for a specific port.
- Advanced: Configure a rule for a range of addresses on specific ports.
The easiest method is to use the Preconfigured tab. From this tab, all that is necessary is to select from the different drop-down lists to Allow/Reject/Deny/Limit on Incoming/Outgoing traffic for a Program/Service.
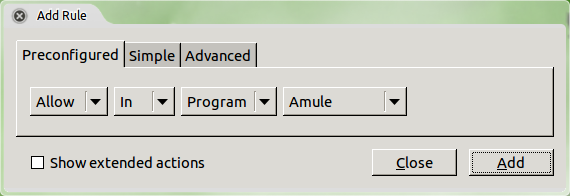 If you need more actions, click the Show extended actions check box.The Preconfigured tab allows for the Allowing/Denying/Rejecting/Limiting of the following Programs:
If you need more actions, click the Show extended actions check box.The Preconfigured tab allows for the Allowing/Denying/Rejecting/Limiting of the following Programs:
- Amule
- Deluge
- KTorrent
- Nicotine
- qBittorent
- Transmission
Obviously the developers were more concerned with stopping P2P traffic than any other application. As for services, Gufw offers the following in the Preconfigured tab:
- ftp
- http
- imap
- nfs
- pop 3
- samba
- smtp
- ssh
- vnc
- zeroconf
In order to create a rule from the Preconfigured tab, a selection from each dropdown must be chosen. So, to block all incoming ssh Traffic, the following would be selected: Deny, In, Service, ssh. Once the correct selections are made, click the Add button and the new rule will be listed in the Gufw main window (see Figure 3.)
 Port 22 is the port for ssh, so the rule is correct.
Port 22 is the port for ssh, so the rule is correct.
It should be noted, the Simple tab is similar to the Preconfigured tab, with only one minor variation: Instead of selecting from a drop-down list of services or applications, the port number for the rule will be added via a single text box. A single port or port ranges can be added here, in the form of port (for single port) or port1:port2 (for a port range.) See Figure 4 for an example of a configured port range.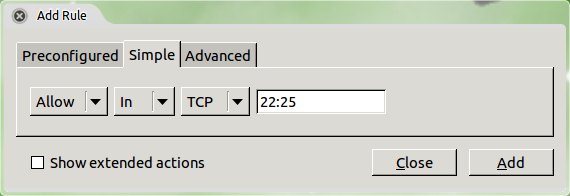
Here ports 22-25 are allowed in.
Advanced Rules
If a more specific rule is required, the advanced tab should be used. Say, for instance, incoming traffic on the internal lan for ssh needs to be allowed only for machines in the 192.168.100.100-192.168.100.120 range. To set this up, the following configuration would be used (The completed entry for the above rule is shown in Figure 5.):
- Allow
- In
- tcp
- From: 192.168.100.100 Port: 22
- To: 192.168.100.120 Port: 22
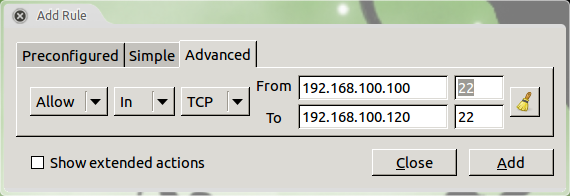
If you make a mistake, the entire rule configuration can be cleared by clicking the “broom” icon.
After the configuration is complete, click the Add button and the rule will be inserted in the rule chain and listed in the Gufw main window. As many rules as necessary can be added and there is no need to restart Gufw as the rules will be live as soon as they are listed in the main window.
Although this is not a lesson on basic firewalling, it is important to remember that a firewall is a chain of rules that every packet is compared against. As soon as a packet matches a rule in the chain, action is taken. So if the Incoming policy is set to Deny, incoming traffic will be denied as soon as it hits that first rule. Sometimes it is easier to allow incoming traffic through via policy and then harden the chain up with individual rules. This takes a lot more time, but will be worth the effort in the end.
Incoming Listening Report
There may be times when it is necessary to view traffic coming in. Why? In my case, I use Dropbox and Ubuntu One for file syncing between computers. My machine also shares printers with everyone on my network. So I need to be able to allow that traffic in. For that I can watch the GUFW Listening Report (see Figure 6) in order to see the specific traffic listed (by Protocol, Port, Address, and Application) and then adjust my incoming rules as needed.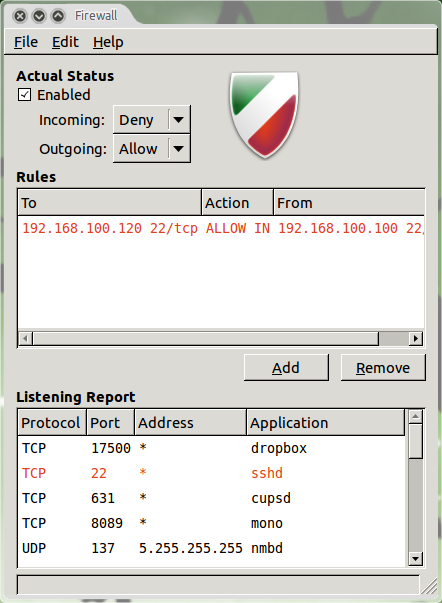
The listening report updates in real time.
Configuring Gufw
Gufw does not offer a lot of configuration options. In fact, there is only one single Preferences window offering the following four options:
- Enable Listening Report.
- Enable Gufw logging.
- Eable ufw logging.
- Logging level (low, medium, high, full.)
By default, all options but the Listening Report will be checked. If necessary, the log file for Gufw can be viewed as well. This log file is located in /var/log/gufw_log.txt.
Final Thoughts
The Gufw firewall tool might well be the easiest firewall tool available for the Linux operating system that still offers a modicum of flexibility. Although Gufw isn’t nearly as powerful and flexible as the command line iptables, it does do a very good job of protecting Linux machines from unwanted traffic without having to spend a great deal of time learning a complex firewall rule system.





