While GCC 4.9 is running behind schedule compared to where GCC 4.8 was at this time last year, open-source developers banding together still might get out the GNU Compiler Collection 4.9 release in early April with its many new compiler features…
Do Users Want Freedom from Vendors, or Freedom and Vendors?
 Do you want free software or do you want supported, enterprise grade software? Many people think that’s the question. It’s not.
Do you want free software or do you want supported, enterprise grade software? Many people think that’s the question. It’s not.
Like all data geeks we wanted to understand the appetite by the networking industry for open source SDN and NFV, so the OpenDaylight Project commissioned a report from Gigaom Research that was made available today. It surveyed enterprises and service providers across North America to understand network pain points and where SDN and open source could help. What struck me was that 95 percent showed a strong bias for open source, and 76 percent said they want to consume open source from a commercial vendor. Does this seem at odds? Not at all. This isn’t wanting your cake and eating too. It is fully rational to want both. The report clearly illustrates an evolution that’s happened in the software industry where people want the best of both worlds: the flexibility, freedom and neutrality of an open source solution with the advantages of support and services that a commercial vendor can provide. Of course many will want to consume at the extremes (fully proprietary or fully open) and that’s fine too. I call the emerging dominant model Open Plus, and you can read more thoughts about that here.
Report: SDN, NFV, and Open Source: The Operator’s View, March 2014
Difference Between su Vs sudo and How to Configure sudo in Linux
Linux System is much secured than any of its counterpart. One of the way to implement security in Linux is the user management policy and user permission. normal users are not authorized to perform any system operations. If a normal user needs to perform any system wide changes he needs to use…
[[ This is a content summary only. Visit my website for full links, other content, and more! [[
Ubuntu Now Runs Well On The MacBook Air, Beats OS X In Graphics
While last year I wrote how running Ubuntu is messy on the 2013 MacBook Air, when trying out Ubuntu 14.04 LTS on the Intel Haswell-based MacBook Air with HD Graphics 5000, it’s a very different story. Not only is Ubuntu Linux now running on the MacBook Air without show-stopping issues, but its OpenGL performance can even beat Mac OS X 10.9.2.
Risk Assessment / Security & Hacktivism 10,000 Linux servers hit by malware serving tsunami of spam
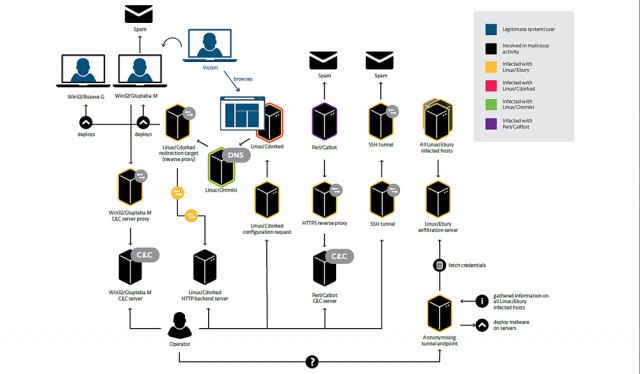
Researchers have documented an ongoing criminal operation infecting more than 10,000 Unix and Linux servers with malware that sends spam and redirects end users to malicious Web pages.
Windigo, as the attack campaign has been dubbed, has been active since 2011 and has compromised systems belonging to the Linux Foundation’s kernel.org and the developers of the cPanel Web hosting control panel, according to a detailed report published Tuesday by researchers from antivirus provider Eset. During its 36-month run, Windigo has compromised more than 25,000 servers with robust malware that sends more than 35 million spam messages a day and exposes Windows-based Web visitors to drive-by malware attacks. It also feeds people running any type of computer banner ads for porn services.
The Eset researchers, who have been instrumental in uncovering similar campaigns compromising large numbers of servers running the nginx, Lighttpd, and Apache Web servers, said the latest campaign has the potential to inflict significant harm on the Internet at large. They explained:
The number of systems affected by Operation Windigo might seem small when compared with recent malware outbreaks where millions of desktops are infected. It is important to keep in mind that, in this case, each infected system is a server. These usually offer services to numerous users and are equipped with far more resources in terms of bandwidth, storage and computation power than normal personal computers. A denial of service attack or a spam-sending operation using one thousand servers is going to be far more effective than the same operation performed with the same number of desktop computers.
Nokia Tries to Lure Android Porters with Free Nokia X Mobes
In London? Fancy a free beer?
Event Nokia has started encouraging Android developers to support its Nokia X platform. The phones, primarily aimed at developing markets, run a highly customised version of Android and to ensure compatibility Nokia has wound up its developer outreach programme.…
Two-Factor Authentication (One time passwords by SMS) for SSH and more
With passwords becoming inherently insecure nowadays, I decided to add an extra layer of security by using the Textlocal One-Time Password API (Its so new I haven’t been able to get it documented yet).
One-Time Passwords are unique codes which are sent to a trusted mobile device which can then be checked and then allowed or denied access based on the response back.
This is pretty awesome considering the code can not be guessed, expires after 24 hours, can only be used once, and is separate to the service which is requiring the authentication.
Like I said, I decided to add One-Time Passwords to my Linux server, to do this, I added the following code to the bottom of my user’s (my user, since no other users have SSH access) .bashrc file:
tlrequest="username=**EMAIL**&password=**PASS**&numbers=**NUMBER**&message=SSH%20OTP%20is&sender=SSH-OTP"
trap logout INT
curl -s -d $tlrequest http://api.txtlocal.com/otp_send >/dev/null 2>&1
echo "A One-time password has been sent to your device. Please enter it below followed by [enter]:"
read otp
check=$(curl -s "http://api.txtlocal.com/otp_challenge/?username=**EMAIL**&password=**PASS**&numbers=**NUMBER**&code=$otp >/dev/null 2>&1")
if [[ $check == *uccess* [[
then
echo "OTP Validated.";
else
echo "OTP Invalid. Disconnecting."
logout
fi
To make the code work, you will need:
1. A Textlocal account
2. Change **EMAIL** to your email address
3. Change **PASS** to your Textlocal password or hash
4. change **NUMBER** to your mobile number (eg 447000000000)
Thats it!
One Week Left To The 2014 Linux Foundation Collaboration Summit
Kicking off one week’s time will be the annual Linux Foundation Collaboration Summit in Napa Valley, California…
IBM, New York Genome Center Prep Watson Prototype
The collaboration, one of many IBM is planning to widen cognitive computing’s footprint, will be the first Watson implementation for genomic research.
Our Many Performance Benchmarks Of The Linux 3.14 Kernel
In complementing the earlier article about the top changes of the Linux 3.14 kernel that will be released in the days ahead, here’s a list of our many exciting Linux 3.14 kernel benchmarks that have been conducted to date…
