If you love technology, you can find a space for yourself and connect with others around mutual interests, according to Avni Khatri, president of Kids on Computers (KoC), a nonprofit that sets up computer labs using donated hardware and open source software in areas where kids have no other access to technology.
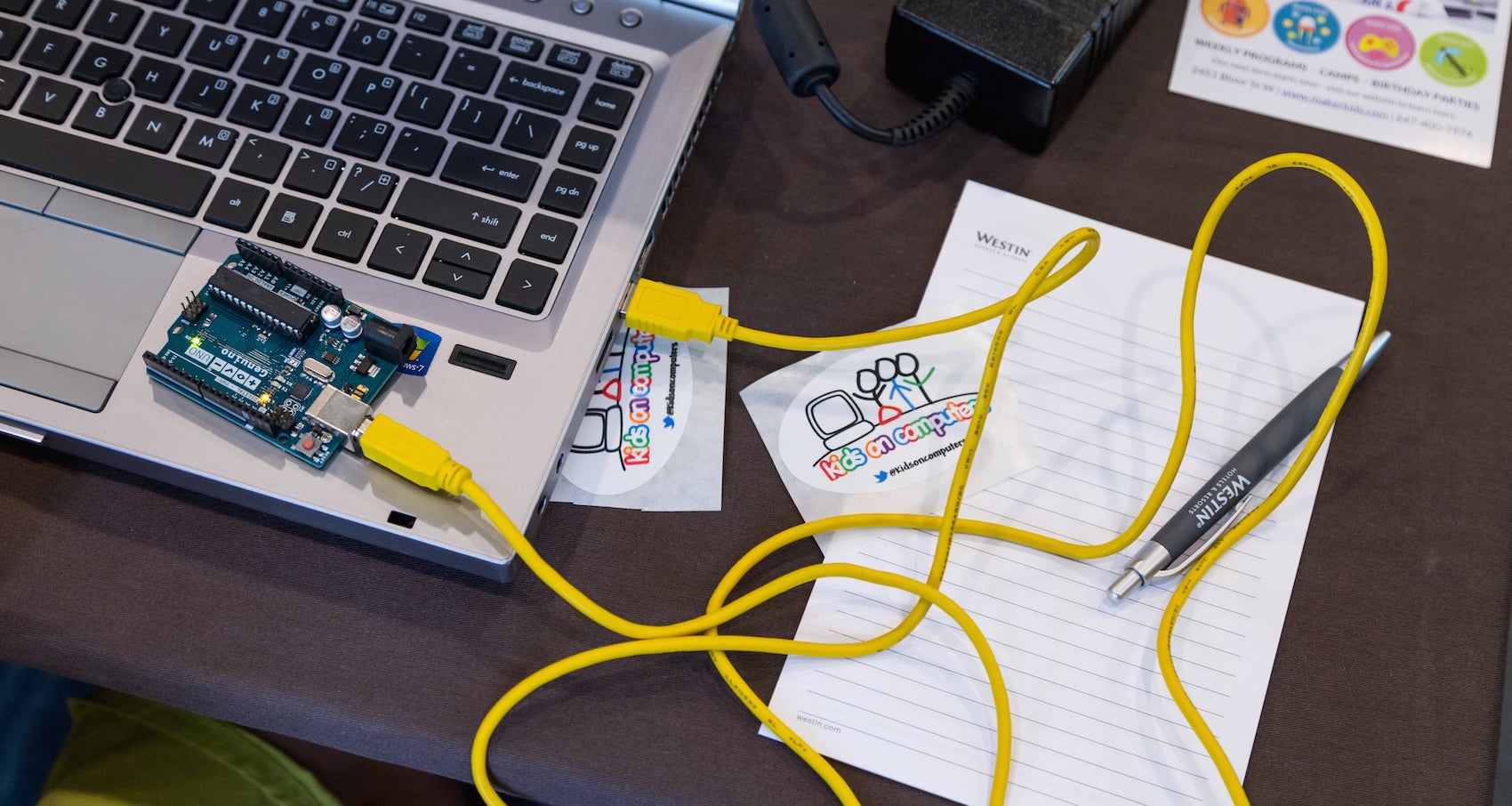
During LinuxCon North America 2016, Khatri organized Kids Day, a day-long workshop that’s aimed at helping school-aged children get interested in computer programming. For Khatri, it’s also a way of furthering her dream of giving children unlimited access to education and helping them succeed in technology.
“The key is to find what you are passionate about and work in that space,” she said. “For me, Kids on Computers is that place. The organization has transformed my thoughts on how much impact I can have in the world. It’s shown me that a little can go a long way (though there is a lot more to do!), and I always have it within me to give.”
“Find your community and connect with them on a regular basis,” advised Khatri.
Although Khatri has been working with the KoC project since 2010, in her day job, she is Program Manager of the Knowledge and Technologies Group in the Massachusetts General Hospital Laboratory of Computer Science. There she helps build bioinformatics applications using open source software and hardware.
“My interests include studying different learning methodologies and researching and implementing different technologies and modalities to deliver learning content, said Khatri in an interview.
Before working at MGH, she was a Front-End Engineer on the Flex Force Tiger Team at Yahoo! Inc. “Engineers on the team are deployed to work in 3-6 month cycles on the highest priority projects at Yahoo! I was also co-president of the Southern California chapter of Yahoo! Women in Tech,” she said.
Khatri, who has a BS in Computer Science from Cal Poly Pomona, has been working on computers for a very early age. “I learned to program in BASIC when I was 11 and started working building database-backed web sites when I was 19,” she said.
She started contributing to open source while at Arsdigita back in 2000, where they developed a framework that allowed people to build community-based web sites easily and included standard packages that one would expect in groupware. The product eventually became OpenACS and Khatri was elected to the Technical Committee and became more involved. “I learned the value of FOSS and how it can help bridge and connect virtual and real-world communities,” she said.
Real world challenges for women in tech
Khatri thinks that one of the challenges women engineers in particular face is feeling alone. “Women engineers are in a significant minority on engineering teams and it can be hard to be the only woman on a team of 5 or 10 engineers,” she said.
Her dream is that everyone, especially kids, get unlimited access to education so that they can decide for themselves what their lives should be so they can improve their own lives and the lives of their communities. This aligns with the mission of KoC perfectly. “Because of my belief in the vision, I am able to focus on the organization and work my way through challenges that arise.”
When talking about inspiring and motivating others, Khatri advises: listen to them and be inclusive. Most of the time we don’t listen to learn, we listen to respond, but Khatri believes that “understanding people’s goals and seeing if you can help is one way to motivate and inspire them. I believe that everyone needs to find out what works for them and supporting people in their self-determined goals goes a long way towards retaining them as volunteers in a FOSS organization or anyplace.
Interested in attending Open Source Summit North America on September 11-13? Linux.com readers can register now with the discount code, LINUXRD5, for 5% off the all-access attendee registration price. Register now to save over $300!