Home Search
live - search results
If you're not happy with the results, please do another search
GCC: Optimizing Linux, the Internet, and Everything
Software is useless if computers can't run it. Even the most talented developer is at the mercy of the compiler when it comes to...
How Linux Is Changing The Face Of End-User Computing
End-user computing (EUC) is changing quickly, and dramatically. In my work, I hear just how vital it is that organizations deliver better security, manageability...
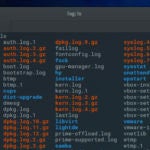
Open Source Logging Tools for Linux
If you’re a Linux systems administrator, one of the first tools you will turn to for troubleshooting are log files. These files hold crucial...
Continuous Security with Kubernetes
As the Chief Technologist at Red Hat for the western region, Christian Van Tuin has been architecting solutions for strategic customers and partners for...
Top Five Reasons to Attend Hyperledger Global Forum
In just over two months, the global Hyperledger community will gather in Basel, Switzerland, for the inaugural Hyperledger Global Forum.
With business and technical tracks...
What Comes after Moore’s Law?
The literal meaning of Moore’s Law is that CMOS transistor densities double every 18 to 24 months. While not a statement about processor performance per se,...
Netrunner Builds on KDE for a Unique Linux Spin
Most every Linux distribution is based on another one. Many are based on Ubuntu or Debian, some are based on Fedora, while others are...
How Github Can Be The Most Powerful Ticketing Tool
How Github Can Be The Most Powerful Ticketing Tool
Compared to all other ticketing tools, GitHub Issues is the only platform giving entire freedom to...
Redefining Security Technology in Zephyr and Fuchsia
If you’re the type of person who uses the word “vuln” as a shorthand for code vulnerabilities, you should check out the presentation from...
Working with Linux File Links
In this article by Oliver Pelz, the author of Fundamentals of Linux, you’ll take a look at what Linux file links are and how to work with...